Before going on, make sure you meet the requirements:
General recommendations after an Arch install can be found here. I’m going to use this article to collect my list of requirements.
Okay, you have to install sudo.
You also need a user.
And a sudo group.
Use visudo to edit the sudoers file.
groupadd sudo will add the sudo group.
Then you can gpasswd -a drone sudo to add drone to the sudo group.
Then everything works.
Now you can install packages.
ToDo
This list isn’t really in order except for the first one. They are just things that come to mind. Some things I won’t cover, like the fact that you will need something to run X11 before you can have visual programs.
sudo
You’ll need users other than root if you want to drive Arch (or any Linux) in a responsible manner.
It follows that you will need sudo to do anything useful with your system.
Start off by creating a user:
useradd -m -s /bin/bash drone
passwd drone
You don’t have to worry about the shell now because we’ll change that when we install oh-my-zsh.
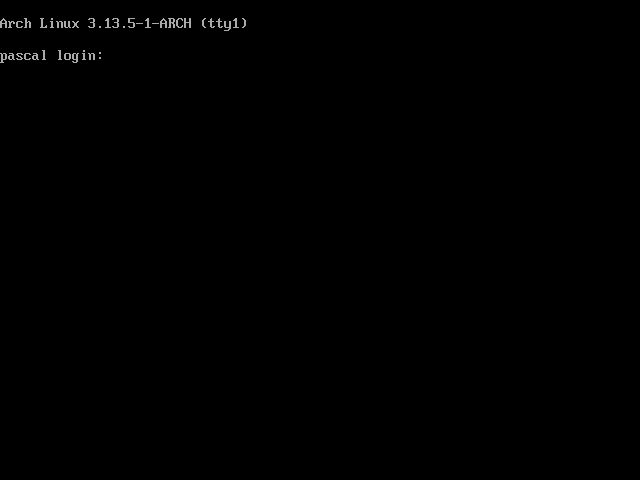
Then you have to install sudo. As root in a TTY:
pacman -S sudo
This will install visudo, which you can use to edit who has access to use sudo. Using visudo, uncomment the appropriate file:
## Uncomment to allow members of group sudo to execute any command
%sudo ALL=(ALL) ALL
Then add your group and add your user to said group:
groupadd sudo
gpasswd -a drone sudo
Then exit root, login as your user and try to escalate something fun.
Audio
It only really makes sense to do this after you have i3 installed.
sudo pacman -S pulseaudio
pulseaudio start
And then I think everything just worked. I have my i3 config configured thusly to get my buttons to work.
~/.config/i3/config
bindsym XF86AudioRaiseVolume exec --no-startup-id pactl set-sink-volume 0 +5% #increase sound volume
bindsym XF86AudioLowerVolume exec --no-startup-id pactl set-sink-volume 0 -5% #decrease sound volume
bindsym XF86AudioMute exec --no-startup-id pactl set-sink-mute 0 toggle # mute sound
# Pulse Audio Controls
Network Manager
This is a real joy. Single line connecting to WiFi. Back in the day, this was a horror story of loading kernel modules and hoping that it worked. I am really happy that Linux had come for enough that I can search the Internet for solutions while I’m bootstrapping a new system.
Install networkmanager and optionally the VPN plugin.
sudo pacman -S networkmanager networkmanager-openvpn
sudo su
systemctl enable NetworkManager.service
systemctl start NetworkManager
nmcli device wifi connect "FBI PARTY VAN" password "hunter2"
That’s it! Just keep adding connections!
Fonts
OH GOD. Don’t fuck with this. I don’t think you know pain until everything you touch, including TTY, IS DISPLAYED IN FUCKING OSWALD. I wish I had my screenshot capability at the time that I was fighting with this because it hilarious now that I have recovered.
Honestly, there were so many things I tried, and I don’t have a coherent order for how I got it working. I’ll try to tell you what not to fuck up.
fc-list : file | grep "[some font you care about]" # Look for fonts.
fc-match mono # What font is going to get resolved when you look for "mono"
fc-cache -f # Cache all fonts
/usr/share/fonts # Font collections
/etc/fonts/conf.[d|avail] # Active and available fonts.
Those two folders at the end work like other daemon configuration.
You have active fonts in /etc/fonts/conf.d an you have available ones in /etc/fonts/conf.avail.
I was only able to get things to work by symlinking all thins in conf.avail in conf.d.
I don’t know how these files really work and I don’t think I have the time right now to figure it out.
After looking at it more, I have no idea how my fonts are working, and I really don’t want to touch it.
Theoretically, /etc/fonts/local.conf should point to my default fonts, but I have uncommented everything in that file.
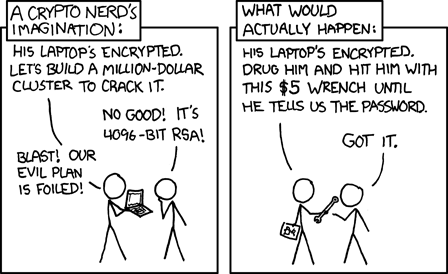
Rotating LUKS Keys
Be careful playing with crypto keys. Be brave though.
You have 8 key slots to work with. You can add a key using the following block. It will prompt you for any existing password and then add the new one.
sudo cryptsetup luksAddKey /dev/mapper/MyVol-cryptroot
You can use this to see information about which key slots are populated.
sudo cryptsetup luksDump /dev/mapper/MyVol-cryptroot